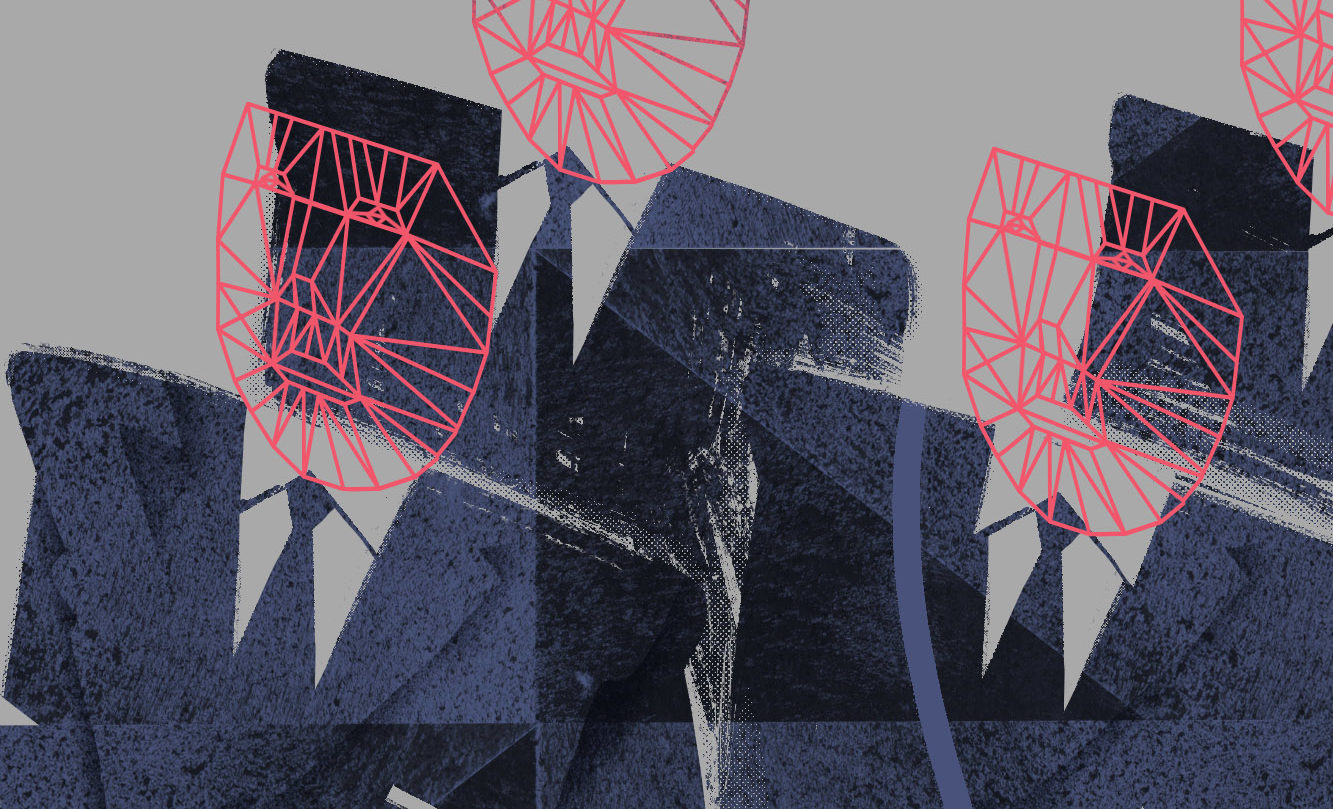
Surveillance technology might be even more invasive than we think. According to new research published by a Norwegian student, some models of Bluetooth headphones can be used to track and identify their owners without their knowledge.
Bjorn Martin Hegnes, 35, who studies networks and IT systems at Norof University in Oslo, undertook a 300km cycle ride around the Norwegian capital over 12 days as part of his first year project. His kit included an omni-directional Wi-Fi antenna that could pick up Bluetooth signals from a distance of 100 yards away and a GPS device that could pinpoint locations.
Hegnes was able to collect around 1.7 million Bluetooth messages, over 9,000 Bluetooth transmitters and 129 headsets.
He discovered that none of the headphones he analyzed during his cycles were implementing a security measure known as media access control (MAC) address randomization, which made it easy for him to pinpoint the exact locations of wearers.
We spoke to Hegnes about his research and how it highlights vulnerabilities in everyday devices.
This conversation has been edited for length and clarity.
Coda Story: What kind of devices did you observe and which were the most vulnerable to tracking?
Bjorn Martin Hegnes: Think about every accessory we are connecting to our smartphones, like smart watches and headphones. Headphones are the easiest to track because they’re broadcasting the name of the device and many people use their first, last or full name on their headphones. These devices that people use in daily life without thinking are easy to track. There are also other things like electric toothbrushes and weight scales. I even found a coffee mug. I had data points on the person who had that mug.
The reason why some digital devices can be tracked over time is because they don’t change their MAC address. What is that, exactly?
A MAC address is like a hard-coded number in a device that can identify you. It’s like an IP address that never changes. I showed in my project that when you have enough data points, you can find where the person goes to school, where he lives. You can get a lot of information from a person that has a static MAC address on their devices. One person in my class had 21 data points on him. You could pinpoint where his apartment was, then you had different data points on his surroundings and his neighborhood, where he goes for coffee and groceries.
Your report says that it appears to be easier to track the movements of an individual via a Bluetooth headset than it is via a smartphone. Why is that?
From what I understand, smartphones went from having static MAC addresses to random ones after the Edward Snowden leaks, which stated that the NSA had tracked people’s smartphones with their MAC addresses. But a lot of headphones are still using a static address — even new ones. The project showed that it was harder to find phones to track. Headphones were much easier.
How can this MAC address be captured?
If you have an Android phone, you can go to the App Store and download a free app called WiGLE. That’s how I started. It will track everything for you
What surprised you most about your research?
That you can easily mass track a whole city on a really low budget. My device cost around two to three hundred bucks. I was really surprised. When I told people how little money I spent, they were shocked too.
So to recap, why do you think the vulnerability of these devices is important?
The privacy concerns are that somebody can track you without your knowledge. You can have good security on your phone and turn off your location data on all of your apps. But a lot of people are not aware that using things like wireless headphones leaves them vulnerable.
What can we do to protect our privacy?
One thing is to keep generic names on your devices, so they don’t include your name. If you have serious concerns about your privacy, stop using devices that don’t support the randomization of MAC addresses. Go back to using wired headphones.