On November 24, Aziz Karimov, a journalist based in Baku, received an email from Facebook notifying him of a request to reset his password. Karimov knew something was wrong since he hadn’t requested a password change. Ninety minutes later, as he struggled to regain access to his account, he received four more notifications from Facebook. He was informed that he had also been removed as an administrator from four other pages, including one belonging to Turan News Agency, Azerbaijan’s only independent news agency.
“I thought I managed to change passwords but two, three minutes later I saw that I was removed from all of the pages, including the ones I have created myself,” he said.
While Karimov battled the hacking of his accounts, the administrators of another Facebook page, Azadliq Radio, Azerbaijan Service for Radio Free Europe were also hacked. Over the next three to four hours, staff realized they had lost all their video content—over 2,000 videos, posts and photos. The station also lost some 25,000 of its 500,000 followers.
This was not the first time these pages were targeted, nor are they the only media organizations in Azerbaijan to fall victim to hacking. The independent Turan News Agency was targeted by authorities last year and its editor in chief was briefly arrested in a tax-evasion and abuse-of-power investigation. Last January, the Facebook page of the Berlin-based Meydan TV—a news site which covers events in Azerbaijan in three languages—lost control of its Facebook page. During the time the page was inaccessible to its administrators, the channel lost all its posts and one fifth of its 500,000 followers. In all cases, it was eventually possible to restore access to the pages and accounts.
Azerbaijan’s enforcing of limits of control across social media is one example of how governments across the world are placing obstacles to deter the work of journalists and organizers.
The attacker of Karimov’s Facebook account was traced back to an IP address revealed in the email received by the journalist. It was linked to a company called Enginet, a limited liability company describing itself as a multifunction company specializing in advanced information technologies in Azerbaijan. While there is little publicly available information on Enginet, its ownership has been traced to Azerbaijan’s former Chief of the Information Systems Department of the Ministry of Education, Samir Mammadov.
More puzzling was the timing and the reason behind the attack. Azadliq Radio, Meydan TV and a number of other popular opposition and independent online news sites have been blocked in Azerbaijan since early 2017. Although users can circumnavigate the bans using virtual private networks, it is possible the authorities were testing the limits of new surveillance technology with a campaign of online disruption.
Azerbaijan’s enforcing of limits of control across social media is one example of how governments across the world are placing obstacles to deter the work of journalists and organizers. Ahead of elections in Bangladesh in December, authorities suspended both 3G and 4G services across the country for several hours. More recently, in Zimbabwe—amid violent protests against the doubling of the price of fuel—the government blocked all internet access. Zimbabwe Human Rights NGO Forum accused the authorities of cutting off the internet “to mask the massive human rights violations”.
Mike Runey, a senior program officer for Eurasia at Civil Rights Defenders and one of the authors of “Azerbaijan’s digital crackdown requires a political solution” said the attacks were designed to intimidate the media. “Our read was the attacks were meant as the online equivalent of a break-in when burglars ransack the place but leave the safe and valuables untouched,” he wrote in an email. “The goal was to intimidate and drive home the idea that this is not a safe place.”
Other similar hacking attempts have involved Facebook pages of opposition political figures and activists. In the run-up to the snap presidential election in April 2018, former presidential candidate, Camil Hasanli reported losing 75,000 out of 108,350 subscribers of his page and all of the personal posts, videos and articles he had shared since 2013. More recently, on January 20, Ali Karimli, leader of opposition political party Popular Front, reported his personal Facebook page hacked and all its content deleted.
But while attacks on pages of Hasanli could be explained within the context of an upcoming election, the disruption experienced by Karimov and Azadliq Radio is indicative of a new approach which has seen the hiring of more sophisticated hackers equipped with more sophisticated technology to prevent access to independent media and alternative voices.
Disruptive Technology
According to detailed reporting carried out in April 2018, by Virtual Road—a secure hosting project run by the media foundation Qurium, the government of Azerbaijan has been relying on Deep Packet Inspection (DPI) since March 2017. DPI extracts information by allowing digital eavesdropping. If conventional online eavesdropping is like picking up a book and only seeing its cover, DPI allows users to open the book and read it from cover to cover.
According to Virtual Road, Azerbaijan’s DPI equipment was purchased from an Israeli security company called Allot Communications; the same company sold similar technology to Iran in 2011. Reports by Virtual Road have shown evidence of denial of service and other attacks against independent and opposition media news sites, that were traced to IP addresses associated with the government.
In 2014, Citizen Lab revealed that Azerbaijan was among 21 countries using Remote Control System (RCS), another form of surveillance technology that allows for data collection on infected devices both online and offline. Other countries suspected of using RCS include Colombia, Egypt, Malaysia, Saudi Arabia, Turkey and Uzbekistan. The data is obtained through records by keystroke loggers and the system also allows hackers to turn on device cameras and microphones without the user’s knowledge.
Trolling and Spear Phishing
While spear phishing and hacking of social media accounts are two common ways to impede the work of journalists and activists, other forms of digital intimidation and surveillance include impersonating accounts, takedown requests, trolling and blackmail.
One recent incident saw a reporter from Azadliq Radio pressured by a harasser called Teyyub Khalilov on Facebook messenger to reveal information about her colleague. This happened shortly after the radio station’s Facebook page was hacked. Although Khalilov’s account was taken down by Facebook after six hours, the incident impacted the journalist and her colleagues.
Organizations who find their Facebook pages repeatedly attacked eventually move to other mediums, which can adversely impact their audiences.
State-sponsored trolling has also been widely employed over the past few years. Content which originates from trolls gathers around certain events, such as elections, referendums and political rallies when trolls copy and paste articles including speeches given by the president and other officials in pro-government media. They also engage in spear phishing in comments under Facebook posts and YouTube videos. When a Facebook page is hacked, its new owners spare no time in sending out malicious or infected links.
The same patterns can also be seen in other authoritarian countries like Russia and Ecuador. In the Philippines, Rodrigo Duterte used trolls to work for his 2016 presidential campaign. Political groups in India like Prime Minister Narendra Modi’s Bharatiya Janata Party can mobilize thousands of members to attack political opponents.
The effects of state-sponsored disruption of online services are not solely limited to censorship. Organizations who find their Facebook pages repeatedly attacked eventually move to other mediums, which can adversely impact their audiences. “People organized before the current iteration of social media and will do so after, so even if Azerbaijani Facebook becomes so dangerous or toxic that people abandon the platform, it will just move to another medium”, said Runey, in an email to Coda.
“At the end of the day, however, this isn’t solely about finding technological solutions to these technological problems. Even extremely repressive and authoritarian governments recognize this, or will have to eventually, which is why China has, despite deploying unprecedented tools of 21st century mass surveillance and intimidation in Xinjiang, resorted to the 20th century tool of mass internment camps.”
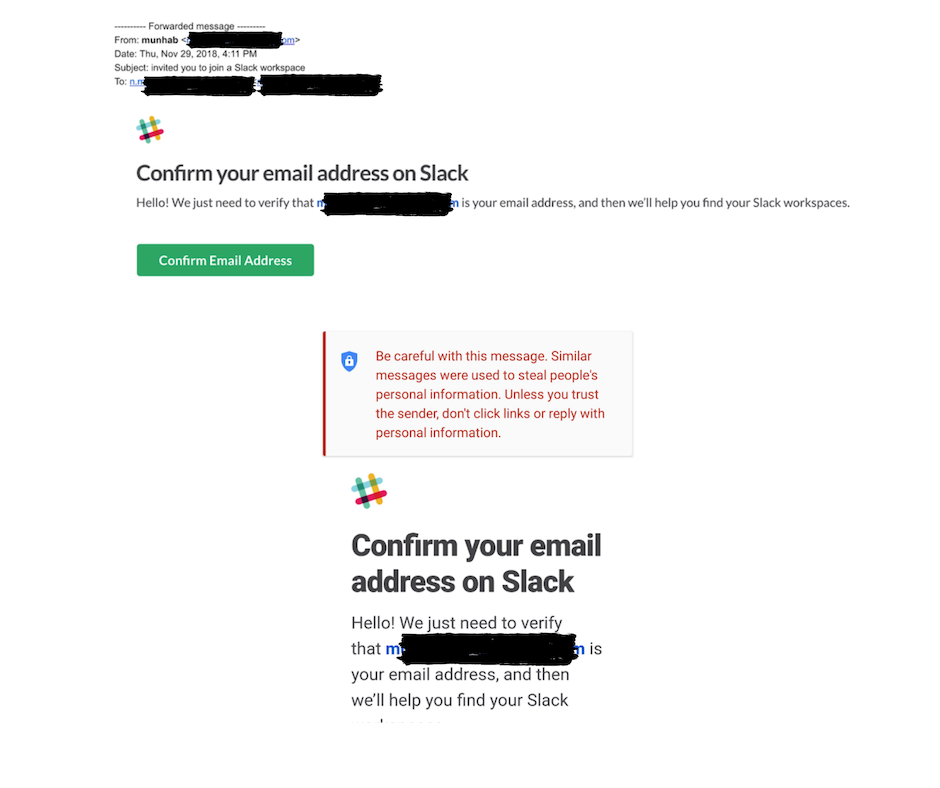
On November 29, human rights lawyer Nijat Mammadbayli received an email from an individual purporting to be Hebib Muntezir, the social media manager at Meydan TV. The email appeared to have been sent from Slack but asked Nijat to confirm that [email protected] was Hebib’s email address. Mammadbayli knew this was a trap and when he went to check the email again a few days later, the email contained a warning, “Be careful with this message. Similar messages were used to steal people’s personal information. Unless you trust the sender, don’t click links, or reply with personal information”.
The YouTube channels of independent and opposition media outlets are also often subject to targeted attacks. Last July, “Azad Soz” (Free Speech) was blocked on YouTube after receiving three strikes, due to “copyright violations”. The alleged source of the takedown request originated with the Ministry of the Interior, however, the email address cited on the request pointed to [email protected], not the official email of the Ministry of the Interior—[email protected]. Hamam Times is another popular YouTube channel that faces takedown requests on a regular basis.
Journalists say Azerbaijan’s disruption of the internet, using laws and malware attacks to hamper the work of civil groups and independent voices, ultimately damages trust in the media.
“When attacks take place, they weaken the trust public has vested in us,” said Meydan TV social media manager Hebib Muntezir. “We receive all kinds of information and leaks from our audience, but once our accounts are compromised or hacked and their personal information is exposed, we endanger them, the trust suffers”.