In late 2020, a cancer charity contacted the U.S.-based cybersecurity company, GroupSense, in a panic. One of the world’s largest cybercrime gangs had infiltrated the organization’s computer system and kidnapped its data. An ominously worded message explained that the hackers were willing to restore the nonprofit’s records in exchange for several million dollars.
The digital ambush thrust the charity into uncharted and potentially catastrophic territory. Paying the requested amount was unthinkable for a nonprofit group, and even if it were able to foot the bill, news of the breach trickling out to donors could be devastating. The organization eventually turned to GroupSense, which has carved a niche out of negotiating ransom payments between hackers and victims, for help.
“They were like, the number is so far off the mark that this seems hopeless. We’re doomed,” said Kurtis Minder, the company’s founder and CEO.
The middlemen agreed to step in.
Wrangling with the subterranean world of cyber-hijacking requires some finesse. So, GroupSense created a set of principles to guide their conversations. “Don’t be antagonistic, be polite and treat it like a business transaction,” explained Minder. But this case tested the organization’s patience. “We were so angry,” he recalled. “We were like, ‘You hit a cancer charity. They don’t have any money. You should just unencrypt their files immediately, so they can go back to saving people.” The appeal to the hackers’ better angels was ignored, but the two groups were, eventually, able to settle on a much lower fee than the original demand: $10,000.
The incident provides a glimpse into a dawning era of cyber chaos, where unscrupulous actors are seizing upon the vulnerabilities of our digital world in increasingly brazen and frequent attacks. Some are doing so via ransomware, a form of malicious software that hackers deploy to encrypt victims’ data and then extort them for payment.
From 2019 to 2020 alone, ransomware attacks rose by 62% globally and 152% in North America, according to a report by the cybersecurity firm SonicWall. Hackers have slipped into the electronic networks of schools, hospitals, voting systems, local governments, small businesses, and major food and fuel suppliers, disrupting the lives of millions of everyday people — all as the coronavirus pandemic cements a shift toward an ever-increasing reliance on digital systems.
The data suggests that we have entered a new phase of digital disruption. While nobody can predict what the future will hold, the evolution of disinformation could provide a useful guide. A decade ago, the issue was barely on people’s radar; now, it has become so ubiquitous in political and technological debates that a world without it seems almost unimaginable. Could ransomware follow a similar trajectory?
Disinformation and ransomware share an ability to fracture the body politic. Both can sow instability, chip away at social cohesion, and compromise peoples’ faith in institutions. There is also a clear geopolitical dimension to both.
“They’re both of a piece — world politics slowly grappling with the realization that all information is strategic,” explained Ryan Williams, a PhD student in public policy at The University of Texas at Austin. “And the state that can best harness the implicit value of the data that’s all around us is going to be able to project their will more effectively.”
To be sure, there are some key differences between the two. As the name suggests, ransomware is an explicitly profit-driven exercise — the whole system is built on extorting money via the kidnapping of data. That’s why there is a consensus among many cybersecurity experts that the people and entities behind ransomware are largely motivated by financial gain. The distinction doesn’t mean that the politics and profit of ransomware are mutually exclusive. Governments can benefit from attacks they don’t order, and attacks of a large enough magnitude — for example, targeting critical infrastructure projects — can inflame geopolitical tensions, even if carried out by individuals and groups not affiliated to the state.
The ransomware ecosystem is made up of murky criminal groups whose origins and intentions can be difficult to trace. But negotiators like Minder get a rare glimpse into the anatomy of attacks and the bureaucratic machinery of some of the large cybercrime syndicates that carry them out.
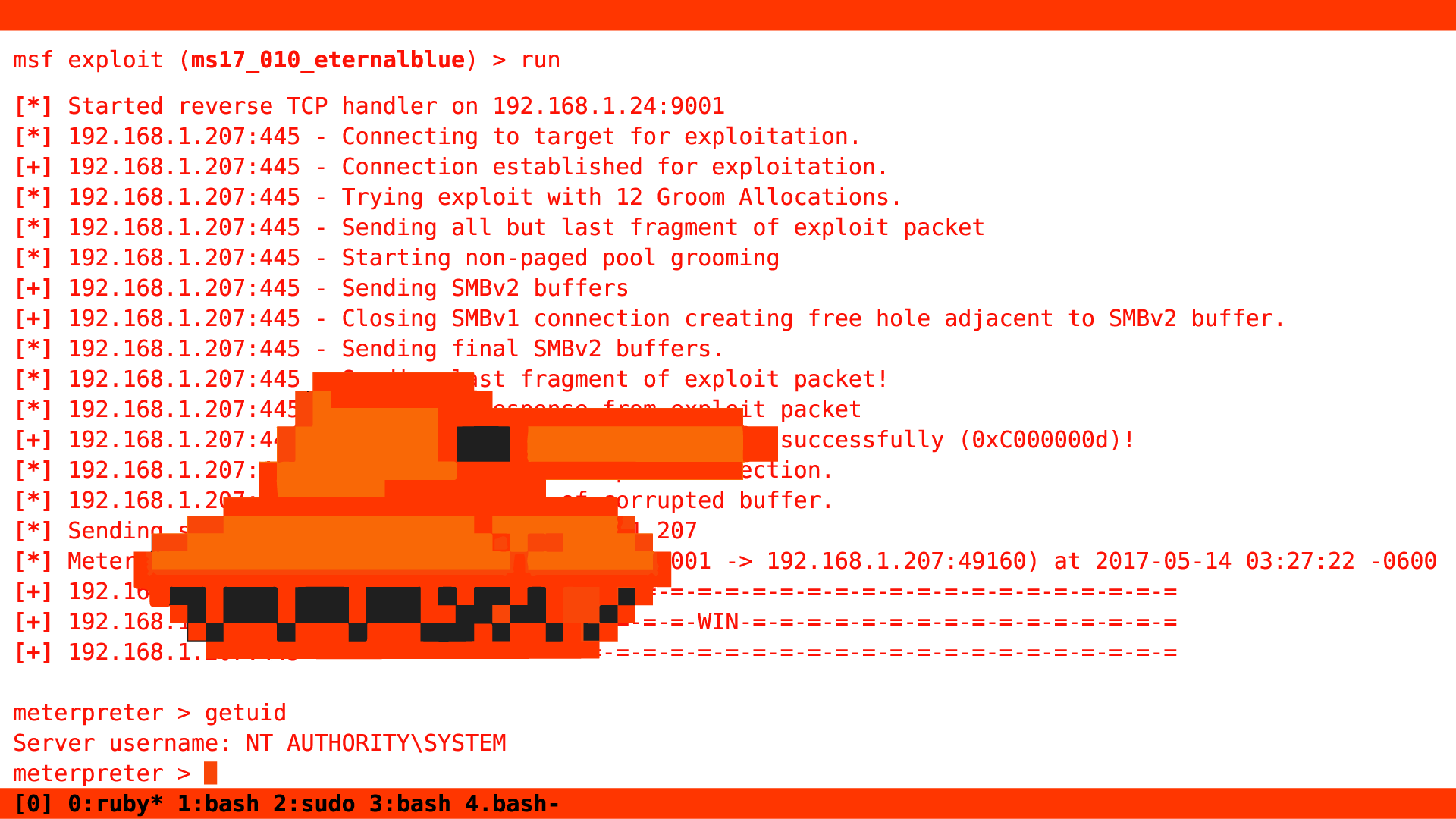
Hacks usually take a similar shape: Someone tries to log in to their company or organization’s computer system and, instead, finds a note telling them that their data has been taken hostage and with instructions for how to get in touch, often via a chat on the dark web. Navigating to the suggested page may bring up a digitized clock counting down the amount of time a target has to comply with a ransom demand before attackers up the ante — like notching up the fee or wiping out a percentage of their data.
At some point in this process, Minder, who is 44, chatty, and surprisingly upbeat for someone who spends a significant chunk of his time submerged in the bowels of the internet, will step in to mediate. Although he’s spent two decades working in technology and start-ups, Minder’s descent into the dark arts of cybercrime negotiation began about 18 months ago, after GroupSense helped a software company resolve an attack. He agreed to lead the negotiations, and took to it naturally, talking down the ransomware demand significantly. After resolving the case, Minder’s team told him he had a moral obligation to continue helping victims of the growing ransomware industry. The work quickly snowballed. Minder estimates he and his team of two negotiators have handled roughly 100 cases in the last year and a half.
Minder is emphatic that his job is “not sexy. It’s not like I’m jet-setting around, drinking martinis.” Triangulating between victims and hackers can be emotionally draining: imagine trying to help a petrified business owner on the brink of financial ruin; add in a low-level hacker on a different continent whose English is shoddy and is going to need to run your counter-offer by his manager; then multiply that by three — the number of cases Minder typically handles at once. How does he cope with it all? “I probably need to see someone,” he said.
Like a good millennial, I asked Minder about work-life balance. Unsurprisingly, I learned that cybercriminals do not respect the home lives of negotiators. “You know what sucks? The bad guys tend to attack on Friday nights, or before holiday weekends. So, I don’t even plan anything,” he sighed. “Like, it’s Labor Day? I know what I’m doing.” For Minder, who is also a wine enthusiast, even post-work drinks can be a gamble — one too many can jeopardize a delicate negotiation. “If I get a feeling that it’s ok, then I can have a glass at 7,” he said.
Some of the more sophisticated cybercrime syndicates have strict reporting structures. When dealing with them, Minder says his primary point of contact is generally a low-level hacker with limited English who is likely cutting-and-pasting a script into the Dark Web chat and plugging responses into Google translate before passing negotiations off to their manager. “The first person you’re talking to is probably 23 years old,” Minder explained. “And there’s somebody behind them yelling at them. Although Minder deals with all sorts of hackers, he says that many of them appear to be operating out of Russia. “There’s no real mission other than take money,” he said. “They do seem pretty heartless.”
For Minder, the ability to place oneself in the shoes of both hacker and hackee is the one of most important skills in a negotiator’s toolkit. “I think empathy is invaluable,” he explained. “It doesn’t mean sympathy. It means understanding the situation that the person is operating under and the lens that they might look at this through, based on their situation.”
Experts are split on paying off ransomware demands, either directly or via middlemen like Minder. Some — including the FBI, argue that acquiescence motivates cybercriminals to continue launching attacks. Others say the role of a neutral third party is useful in negotiations and can reduce the ransom amount victims end up handing over. Minder is sensitive to opponents’ concerns but realistic about the pressures facing targets. If the choice is between shutting a company down or paying up, “that ransom is probably getting paid with or without me,” he said. “At least we’re going to pay these guys as little as possible.”
Whether you agree with Minder’s position or not, recent events suggest that he is likely to remain busy for some time to come.
Ransomware: Disinformation dressed up in code?
Ransomware is not a new problem, but a spate of recent high-profile attacks points to a criminal enterprise that is becoming increasingly brazen. Just this week, a ransomware attack hit the reproductive health clinic Planned Parenthood Los Angeles, compromising hundreds of thousands of patients’ healthcare data and personal information. Add that to a list of hacks in recent months that have targeted the United States’ largest fuel pipeline, the world’s biggest meat supplier and Ireland’s health care system. In 2020, the U.S. Federal Bureau of Investigation recorded nearly 2,500 ransomware attacks, totaling $29 million in combined losses — up from $9 million in 2019, even though that figure is widely believed to be an undercount.
“Ransomware has exploded into a multi-billion-dollar global racket that threatens the delivery of the very services so critical to helping us collectively get through the Covid pandemic,” Christopher Krebs, the former director of the U.S. Cybersecurity and Infrastructure Security Agency, said in testimony before Congress in May. “To put it simply, we are on the cusp of a global pandemic of a different variety, driven by greed, an avoidably vulnerable digital ecosystem, and an ever-widening criminal enterprise.”
Ransomware attacks have wide-ranging consequences. They can leave small businesses on the brink of financial ruin, threaten election integrity, hobble critical infrastructure, destabilize municipalities, and jeopardize the lives of hospital patients.
Ransomware attacks targeted nearly 2,400 schools, hospitals, and local governments in the U.S. in 2020. In May, hackers took down the sprawling Colonial Pipeline, which runs from Texas to New Jersey, driving up gas prices, causing fuel shortages, and unleashing pandemonium at filling gas stations across the southeast of the country. A 2019 attack paralyzed Baltimore for weeks, preventing people from paying water bills, parking tickets, and property taxes, ultimately costing the city an estimated $18 million. The White House has begun to acknowledge the magnitude of the threat. After the Colonial Pipeline debacle, President Joe Biden signed an executive order aimed at shoring up the country’s cyber defenses and established a ransomware task force to combat attacks.
Richard Forno, director of the graduate cybersecurity program at the University of Maryland, Baltimore County, said the spate of cyber attacks reveals “the fragility of the modern economic and social environment. Our nation is dependent on technology. We’ve built all these infrastructures and services, this digital world we live in, on top of some very flawed foundations.” He likens the contemporary landscape of cyberwarfare to strategic bombing campaigns during World War Two. “You attack a pipeline, you paralyze large swaths of the East Coast. That’s almost as bad as actually physically blowing up the pipeline,” he said.
“Our nation is dependent on technology. We’ve built all these infrastructures and services, this digital world we live in on top of some very flawed foundations.”
The effects of such attacks extend well beyond the practical or financial. Ransomware leaves a mark on our collective conscience, reminding us that the electronic systems that we rely on are vulnerable to widespread disruption at any moment. Maybe it is time to start thinking about ransomware as a form of disinformation draped in code — one that fosters chaos, erodes institutional trust, and inflames geopolitical tensions.Major cyberattacks have also been linked to hackers operating out of Russia, China and North Korea. In July, U.S. officials accused Chinese government-employed contractors of carrying out a massive hack on Microsoft Exchange’s email server, which compromised tens of thousands of computer systems globally, along with ransomware attacks against private companies, prompting NATO’s first-ever condemnation of China’s cyber activities.
In February 2021, the U.S. Justice Department indicted three North Korean intelligence officers over an alleged global hacking scheme aimed at, among other things, stealing more than $1.3 billion from companies and financial institutions, including a 2017 ransomware attack on the U.K.’s National Health Service. Announcing the charges, a U.S. official described the case as a “striking example of the growing alliance between officials within some national governments and highly sophisticated cyber-criminals.” The same month, a report by a United Nations panel found that North Korean cyberattacks totaling hundreds of millions of dollars helped provide revenue for the country’s nuclear weapons program.
Currently, however, the main perpetrators of ransomware attacks appear to be operating out of Russia. According to Josephine Wolff, an associate professor of cybersecurity policy at Tufts University, the country is “the biggest player in the ransomware space and the one that causes the most problems for the United States.”
In June, the FBI accused the Russian cyber gang REvil — reportedly responsible for over 360 attacks on U.S.-based organizations in 2021 — of orchestrating a hack on the world’s largest meat producer, JBS, temporarily hobbling the company’s entire U.S.-based operation. That same month, the crippling of the Colonial Pipeline, which U.S. officials traced to the Russian hacking group Darkside, brought cybersecurity into the spotlight at Joe Biden and Russian President Vladimir Putin’s first face-to-face meeting. “I looked at him and said: ‘How would you feel if ransomware took on the pipelines from your oil fields?’” Biden said in June 2021. The comments prompted a forceful denial from Putin, who argued that most cyberattacks originate in the U.S.
Perhaps the defining feature of Russia’s ransomware landscape is its ambiguity. Experts say it’s extremely difficult to determine if Russia-based hackers are operating at the behest of the government, or merely with its tacit approval. For years, the Kremlin has been accused of giving hackers free rein within its borders, as long as they don’t interfere with government interests or attack Russian targets. (Malware used by REvil is designed to avoid computers that use the Russian language, according to a report from one cybersecurity company). That dynamic allows the government to maintain a posture of plausible deniability about ransomware attacks, attributing them to criminal groups, while potentially benefiting from their outcomes.
“I do think the way that Russia handles this is brilliant,” Minder said. “It’s like, well, it’s not us. It’s just some kids in somebody’s basement. And they are achieving their nation-state goal. A bunch of that money is ending up in Russian banks. And it is highly disruptive to the U.S. economy and productivity. I don’t know that they’re orchestrating it. They just let that monster go.”
After the Colonial Pipeline attack, the Russian-linked Darkside group posted a statement on its website stressing the “apolitical” nature of its work. “We do not participate in geopolitics,” they wrote. “Our goal is to make money.”
Julie Davila, the co-founder of the cybersecurity startup ZibaSec, is understandably skeptical. “What I find curious about people taking the word of some of these syndicates from the dark web is how quickly they trust the random username of some random spokesperson,” she said.
And that unclear line between state and criminal groups moves ransomware into what the PhD student Ryan Williams of the University of Texas at Austin calls “the gray zone of conflict” Because this murky space can prove useful for governments, the future could, in theory, see states increasingly relying on intermediaries to disguise politically motivated attacks as financially driven intrusions carried out by criminals. Such ambiguity also provides fertile ground for the spread of rumor and conspiracy.
“You can imagine the worst-case scenario is an actual cyber-attack on some sort of key electoral infrastructure in an upcoming election that is themed as a ransomware attack from a private actor,” said Williams. “It would just be another huge cycle of really emotionally charged conflicts over the basic facts of our democracies.”