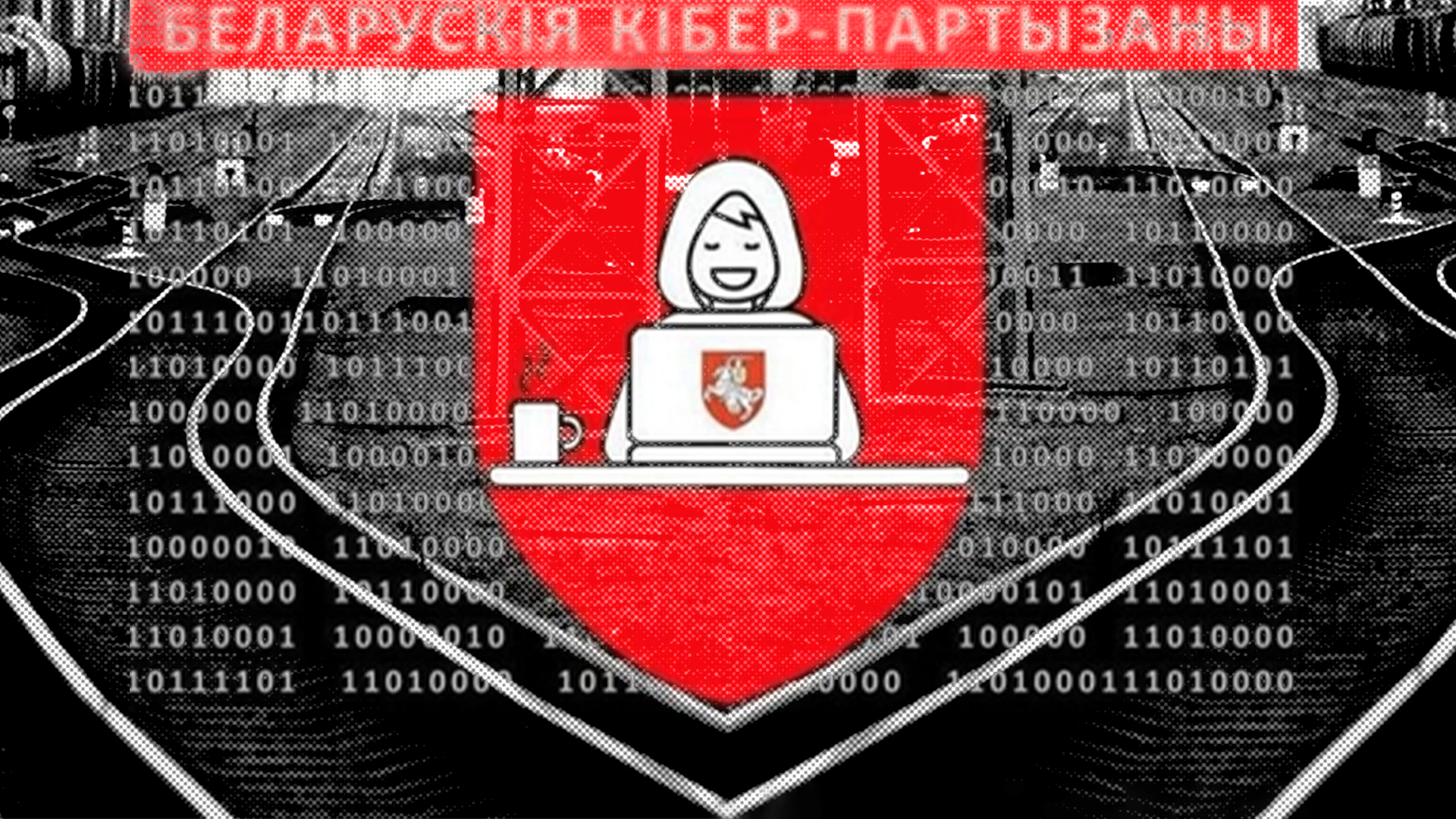
In late January an anonymous group of Belarusian hackers compromised the country’s railway system, claiming it had encrypted some of the state train authority’s databases and destroyed its archives. The group, which calls itself the “Cyberpartisans” says it attacked Belarusian Railway because its tracks are being used to transport Russian soldiers and equipment inside Belarus, near the border with Ukraine.
The Belarusian Railway online ticketing system was temporarily down on the day of the hack, but further consequences are not clear.
“Even Belarusian Railway itself can’t tell the full impact of the attack yet,” said an anonymous representative of the group. “Most of the databases are still not working. We attacked the business intelligence and analytics system so they don’t have the data to fully quantify their losses.”
Last year, the group released troves of tapped phone calls and internal documents from police and interior ministry databases, providing evidence of a brutal police crackdown on protesters following the country’s disputed election in August 2020.
In December the group wrote to Coda Story’s Glenn Kates in a response to a list of questions. Their answers are lightly edited for clarity.
How much of your work is figuring out technical ways to hack into Belarusian databases and sites and how much of it relies on people still working from the inside?
In some instances, we have been getting assistance from insiders that either were part of the system or are part of the system right now. Sometimes they advise on weak spots of different systems, and at other times, they help us with keys and passwords, or open the “backdoor” for us to come into the network, though this is rare. A lot, of course, depends on our skills. We don’t have any members who are or were professional hackers. So in the past year, we have learned how to penetrate online resources, mostly from hacking books and tutorials and a lot of hands-on training. We have failed a lot, learned from our mistakes, and refined our tactics.
How much information do you still have that hasn’t yet been released? Can you give me a preview of any upcoming investigations?
We hacked many government databases and we have a vast amount of data now, so it takes a lot of time to process it. We believe that releasing our discoveries more gradually creates pressure on the regime since, in this case, it’s impossible to ignore us — we are in the news all the time.
The only preview we can give you is our plan to identify fake passports issued for espionage purposes for KGB and other agents who pose a risk to Belarusians in other countries. We are also planning to check all the trips made by Lukashenko and his close circle. This will help reveal illegal activities and put sanctions on them.
Have Belarusian authorities tried to make contact with you? Have any of your members been caught or come close to being caught?
Belarusian authorities never tried to contact us. If they do this to discuss how they can surrender and start the transition of power, we would talk to them. No one has come close to catching us though. Special police forces are, of course, trying to infiltrate us, but nothing has harmed us in any way.
How do you protect the identities of people who send information to you? Can they feel 100% secure sending you information through Telegram?
Yes, we created several tools and released tutorials on how to safely send information to us and to our bigger group, Suprativ, that encourages people on the ground to join the forces of resistance. We have many layers of protection, and it’s safe enough to send us information. The weakest point is the data on any individual’s personal device. That’s why the first thing we do is ask people to start fresh with us and instruct them on how to communicate safely.
We have a special application called Partisan-Telegram, aka P-Telegram, which we developed for the safety of Belarusians. It’s a modification of the original Telegram app. It deletes all the pre-selected chats and channels and accounts from the device upon entry of a false password when trying to access the app. Anyone can read the source code and make sure the app is safe to use.
Why do you use Telegram instead of other encrypted tools, like Signal?
For most secretive communication we use peer-to-peer encrypted tools and platforms. That’s all we can say.
Do you ever worry about getting caught? Do you have a plan for if you are?
We acknowledge that we risk a lot, even probably our lives. However, we can’t just do nothing or stop our work to bring down the regime. We established safe means of communication so if one person gets caught for some reason, others that were connected to that person, won’t be identified.
The Electronic Frontier Foundation says that “privacy is a human right.” Obviously some of your work has destroyed the privacy of your targets. And in just about every country in the world, hacking of government and private sites is illegal. Do you think ethical concerns about the work you do is warranted?
Lukashenko has proved himself unable to have any dialogue with people who disagree with his beliefs. He has threatened many times to destroy people who stand against him and has said that he will never give up power unless he dies.
Our work helps people protect themselves from the brutality of the police forces and resist the oppression from the regime. We put pressure on the government and try to change the regime. We know how much power we have in our hands and how important the security of private information is. That’s why we don’t touch the information of law-abiding Belarusians.
Let’s take a recent post, where you accuse people of being informants against Belarusian protesters. How do you verify that the people you are accusing are indeed the people who did the things you’re saying they did?
Since we hacked the special database that contains everyone who was an informant at some point since the 2020 elections, we made sure that all the names and personal information we released were correct.
I would like to learn a bit about you, without putting you in personal danger. How would you describe yourself as a person? Were you involved in politics or activism before the August 2020 election?
Obviously, we can’t share any personal information. We are a group of different people with different personalities, but what we definitely have in common is the belief that Belarusians deserve a democratic, independent state with the rule of law and protection of human rights.
As a journalist I’ve been overwhelmed by the optimism of Belarusians. Many tell me that despite everything, they are sure that they will win in the end. But few are able to give me a clear description of how that will happen.
In general, our focus is on avoiding physical violence unless we need to defend against imminent danger. We can’t reveal our plans, but we learn from all the well-known revolutions that used nonviolent means of resistance: boycotts, non-cooperation, and non-violent intervention (blockades and occupations). All of this is used and will be used.