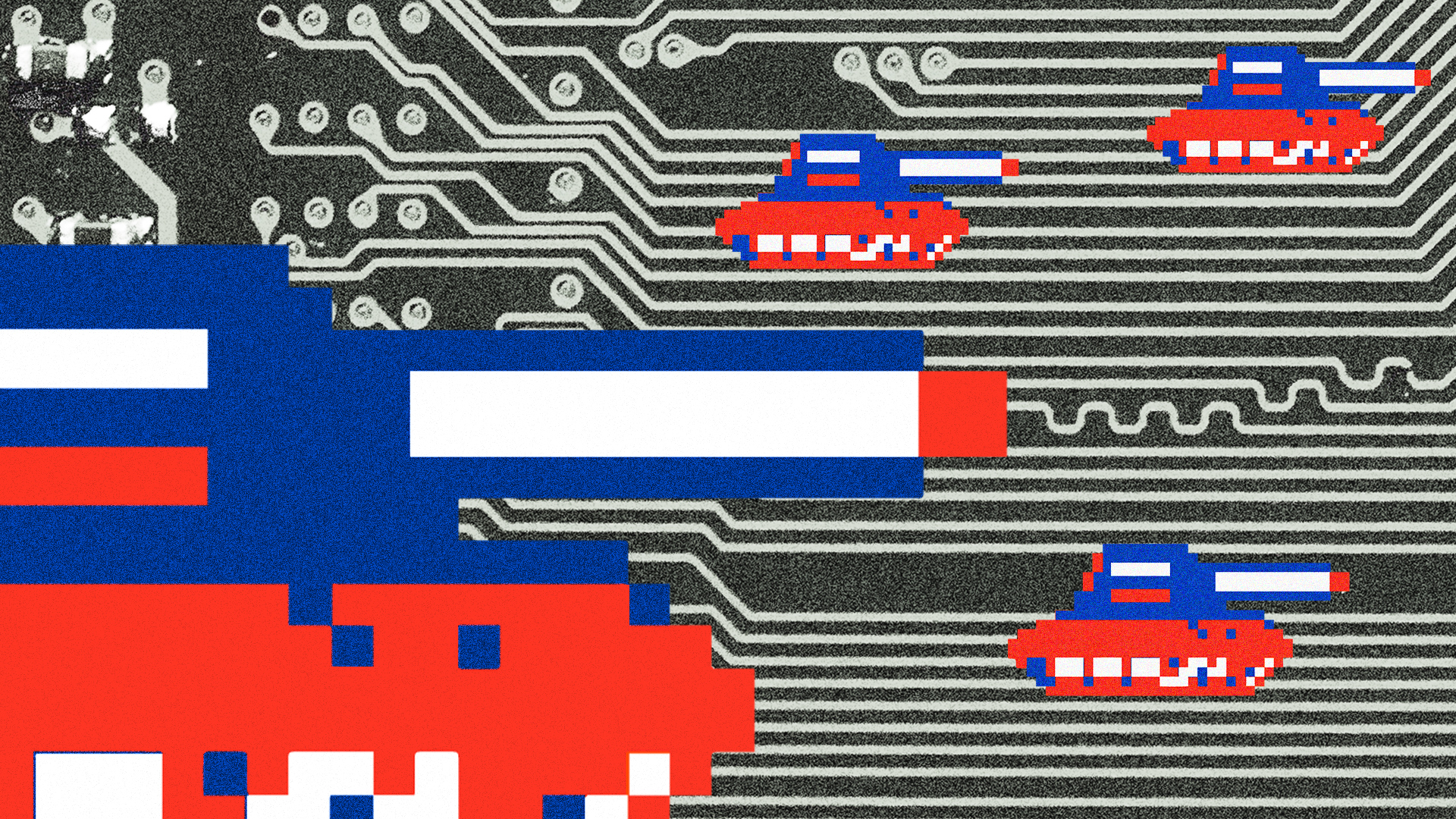
On Thursday morning, as Russia’s invasion of Ukraine escalated, reports surfaced that President Joe Biden was presented with a suite of options for launching a sweeping cyber attack against Russia intended to disrupt its military operations, from shutting off power to disrupting the internet.
The White House vehemently denied the claim, but the report reinforced the cyberwar threat hovering over the Russian invasion of Ukraine. After Biden announced sanctions against Russia on Tuesday, American officials warned businesses and local governments to brace for the possibility of ransomware attacks, which have been held up as a possible strategy for Russia to blunt the impact of sanctions from the U.S. and Europe. Russia is widely known to be a hotbed of ransomware activity.
Ransomware attacks rose by more than 60% globally from 2019 to 2020, and nearly 75% of revenue generated from ransomware attacks in 2021 went to Russian-linked hackers, recent analyses have found. Increasingly, ransomware attacks share the same outcomes as disinformation campaigns, spreading social and political instability, fostering chaos, and eroding faith in government and institutions. As Russia mounts a full-scale invasion of Ukraine, is a global cyber conflict on the horizon?
Richard Forno, director of the graduate cybersecurity program at the University of Maryland, Baltimore County discusses the cyber threat landscape in a conversation that has been edited for length and clarity.
Everything is obviously moving very quickly. There are reports that the Biden administration was presented with options for cyberattacks against Russia, such as disrupting internet access and shutting off power, which the White House then vehemently denied. How are you thinking about this moment and the cyber threat?
I just published an article about the big picture and what this means for cyber in the United States.
In general, the big money quote is this shows that cybersecurity, all cybersecurity, is local. It’s not something that happens in a vacuum on the internet in cyberspace. It has local in-purse ramifications. And geopolitics, i.e., the war, the invasion of Ukraine, events around the world can have cyber consequences here at home.
Not just for large companies and pipelines, infrastructures. But for everybody. Whether it’s a home user whose network might get compromised because they’re working from home, or they’re an individual who can’t fill up their gas tank because there’s been a hack of a pipeline and they can’t get fuel to the gas stations. So, there are a lot of consequences that can result from something that started kinetically, with explosions and missiles and tanks, halfway around the world.
There’s been some conversation about if this could kick off a genuine tit-for-tat cyberwar. What do you think?
I kind of cringe at the word cyberwar. It’s kinda catchy, but the reality is that it’s a tool in a nation’s arsenal. Certainly, Russia and the U.S., in some ways, have shown that they’re not afraid to use it. It’s a tool that can certainly be escalated in its use.
The Russians and Chinese and others have been mapping out our infrastructure for decades precisely to have that knowledge available for situations like this where they might want to escalate.
It could very easily get into a tit-for-tat kind of a situation.
I talked to a cybersecurity expert a few months ago about the risks of geopolitical cyberwar and responding to cyberattacks from other countries in kind, and his position was that it’s very risky because he believes that the U.S.’s defenses around cyber are poor. Do you agree with that?
I totally agree. We, the United States, have always viewed offensive cyber as sort of the cool, sexy aspects of cyber. But cyber defense is kind of routine and boring and an everyday humdrum. It’s not as sexy, not as glamorous. And I think he’s exactly right in this regard. We’ve gotten better over the years, but I think when you look at where the dollars have gone, the interest has gone – political interest – it’s more on the offensive side looking at our adversaries while we continue to have this soft cyber underbelly in our infrastructure. Russia has addressed cyber much more holistically and completely than we have.
Cyber attacks have also targeted Ukrainian government and business websites. Can you explain how they could have effects that ripple outside of the country?
I don’t think it’s one-to-one, like if this happens in Kyiv, this happens in New York. I don’t think that’s the case. One doesn’t necessarily lead to another at a technical level. So Russia launches cyberattacks against the Ukrainian government, banks, etc. Where I see the probability of cyberattacks going beyond Ukraine is if the West retaliates in some way. Then it opens up a Pandora’s box where Russia can say ‘ok, we’re going to come after the U.S., the U.K., other countries and launch cyberattacks that way.’
But if malware is unleashed on Ukrainian companies operating globally, that could cause worldwide damage, couldn’t it?
Oh certainly. If you’re a large multinational company and you’re doing business in Ukraine, you may become targeted intentionally or caught up in an attack and that could have spillover ramifications.
A U.S. official recently warned after the first round of sanctions against Russia that there could be some sort of retaliatory ransomware attacks that could help Russia blunt the impact of sanctions and that’s something companies should be bracing for. Are you concerned about that as well?
Yes. Ransomware continues to be the go-to cyberattack that we’re seeing these days, whether it’s by a criminal group or a nation-state. It would not surprise me to see ransomware attacks launched by Russia or endorsed by Russia. It happened before, in 2015 with the NotPetya attack. Again, that was Russia in Ukraine but it impacted the rest of the world.
Ransomware is one easy attack. I could also see them finding ways to target specific infrastructures, or nodes in infrastructures, to disrupt critical resources. That’s a more labor-intensive approach. With cyber, like with nuclear weaponry, you can’t un-ring the bell. It’s out there.
What do you think is the most responsible thing to be doing at this moment as everything is escalating so quickly for people, businesses, governments, and companies worried about attacks?
The most responsible thing is vigilance. I’ve got a book coming out soon on local government cybersecurity here in the U.S. Nearly one-third of U.S. local governments could not tell you if they’re under attack or have been compromised. That’s pretty scary. You have to be extra vigilant. Not paranoid, but realize that one or two glitches that you didn’t normally expect to see happen, you might want to stop and think is this normal, or am I being caught up in something.
What are you not seeing or hearing discussed in the media in conversations about cybersecurity right now?
What was interesting to me this week is the number of articles and stories in the media talking about cyber. Not just in broad terms but as it affects businesses, and the tone was a little more intimate and personal than I’ve seen similar types of stories during other conflicts over the years.
You look at places like local governments, hospital systems –they’re soft targets. They don’t have deep pockets to hire large cybersecurity teams to monitor networks. They’re left vulnerable in a situation like this were it to escalate even further.
It’s rare to see a cyber story leading the evening news. And yet there it was, I think it was NBC, a cyber warning. You don’t see that too often. And even with the Colonial Pipeline, it wasn’t starting off with here’s the warning from the government. And the tone conveyed to me a different approach than previous media coverage.
It underscores the level of vulnerability we face as a modern society. Here’s an example. I was at the dentist this morning and my dentist told me that on her way into the office, she stopped off to get gas. There were like 10 other cars ahead of her. This is a panic, or a growing panic. What if a cyberattack shuts down gas distribution? How am I going to fill up my car? That’s where cyber meets the real world.
In our ransomware Big Idea, we talked about how these kinds of attacks create mass panic and that can be an important strategic dimension of these attacks. The impact of attacks is not just practical, it’s also psychological.
Exactly, it all feeds in. Cyber is no longer just hackers but includes very much influence and disinformation using cyber capabilities. That’s been happening in Europe and in Ukraine. It keeps us employed.
I think the ball is kind of in the Russians’ court as to what the next steps would be. I would not be surprised to see retaliation of some sort. More economic sanctions were announced this afternoon. There may be some cyber stuff along the way. I don’t know. It’s only 12 hours old. We are in the first innings of this.